It’s been a long, long time since humanity has had a year like this one. I don’t think I’ve ever known a year with such a high concentration of black swans of various types and forms. And I don’t mean the kind with feathers. I’m talking about unexpected events with far-reaching consequences, as per the theory of Nassim Nicholas Taleb, published in 2007 in his book The Black Swan: The Impact of the Highly Improbable. One of the main tenets of the theory is that, with hindsight, surprising events that have already occurred seem obvious and predictable; however, before they occur, no one predicts them.
Example: this ghastly virus that’s had the world in lockdown since March. It turns out there’s a whole extended family of coronaviridae — several dozen of them — and new ones are found regularly. Cats, dogs, birds, and bats all get them. Humans get them. Some cause common colds. Others manifest … differently. So, surely, we need to develop vaccines for them as we have for other deadly viruses such as smallpox, polio, and others. Sure, but having a vaccine doesn’t always help a great deal. Look at the flu — still no vaccine that inoculates folks after how many centuries? And anyway, even to start developing a vaccine you need to know what you’re looking for, and that is apparently more art than science.
So, why am I telling you this? What’s the connection to … well, it’s inevitably gonna be either cybersecurity or exotic travel, right?! Today, it’s the former.
Now, one of the most dangerous cyberthreats in existence is zero-days — rare, unknown (to cybersecurity folks et al.) vulnerabilities in software that can do oh-my-grotesque large-scale awfulness and damage — but they tend to remain undiscovered up until (or sometimes after) the moment they’re exploited.
However, cybersecurity experts have ways of dealing with ambiguity and predicting black swans. In this post I want to talk about one such means: YARA.
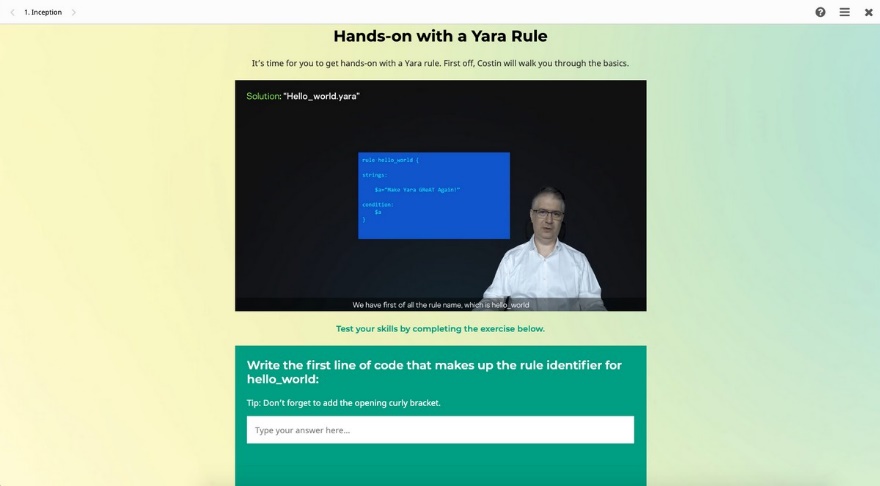
Briefly, YARA aids malware research and detection by identifying files that meet certain conditions and providing a rules-based approach to creating descriptions of malware families based on textual or binary patterns. (Ooh, that sounds complicated. Read on for clarification.) Thus, it’s used to search for similar malware by identifying patterns. The aim is to be able to say that certain malicious programs look like they were made by the same folks, with similar objectives.
OK, let’s turn to another metaphor — like a black swan, another water-based one: the sea.
Let’s say your network is the ocean, which is full of thousands of kinds of fish, and you’re an industrial fisherman out on the ocean in your ship casting off huge drift nets to catch the fish — but only certain breeds of fish (malware created by particular hacker groups) are interesting to you. Now, the drift net is special. It has special compartments, and only fish of a particular breed (malware characteristics) get caught in each compartment.
Then, at the end of the shift, what you have is a lot of fish, all compartmentalized, some of which are relatively new, never-before-seen fish (new malware samples) about which you know practically nothing. But if they’re in a certain compartment — say, “Looks like Breed [hacker group] X” or “Looks like Breed [hacker group] Y.”
Here’s a case that illustrates the fish/fishing metaphor. In 2015, our YARA guru and head of GReAT, Costin Raiu, went full-on cyber-Sherlock to find an exploit in Microsoft’s Silverlight software. You really should read that article, but, briefly, what Raiu did was carefully examine certain hacker-leaked e-mail correspondence to assemble a YARA rule from practically nothing, but that went on to help find the exploit and thus protect the world from mega-trouble. (The correspondence was from an Italian firm called Hacking Team — hackers hacking hackers!)
So, about these YARA rules…
We’ve been teaching the art of creating YARA rules for years. The cyberthreats that YARA helps uncover are rather complex, that’s why we always ran the courses in person — offline — and for only a narrow group of top cybersecurity researchers. Of course, since March, offline training has been tricky because of lockdown; however, the need for education has hardly gone away, and indeed we’ve seen no dip in interest in our courses.
That’s only natural: Cyber-baddies continue to think up ever-more-sophisticated attacks — even more so under lockdown. Accordingly, keeping our specialized know-how about YARA to ourselves during lockdown would have been just plain wrong. Therefore, we’ve (1) transferred our training format from offline to online, and (2) made it accessible to everyone. It’s not free, but for such a course at such a level (the very highest), the price is very competitive and market-level.
What else?
Ah, yes.
Now, given the ongoing virus-related troubles the world over, we’re continuing our assistance to those on the front lines. We started helping out at the start of the whole corona thing by giving free licenses to healthcare organizations. Now we’re adding to that helping out a variety of nonprofit and nongovernmental organizations fighting for rights in various causes or focusing on making cyberspace a better place (the full list is here). For them, our YARA training will be free.
Why? Because NGOs work with very sensitive information that can be hacked in targeted attacks, and not all NGOs can afford the luxury of a department of IT experts.
A quick run-through of what’s included in the course:
100% online, self-paced training. You can do the course intensely in a few evenings or spread it out over a month.
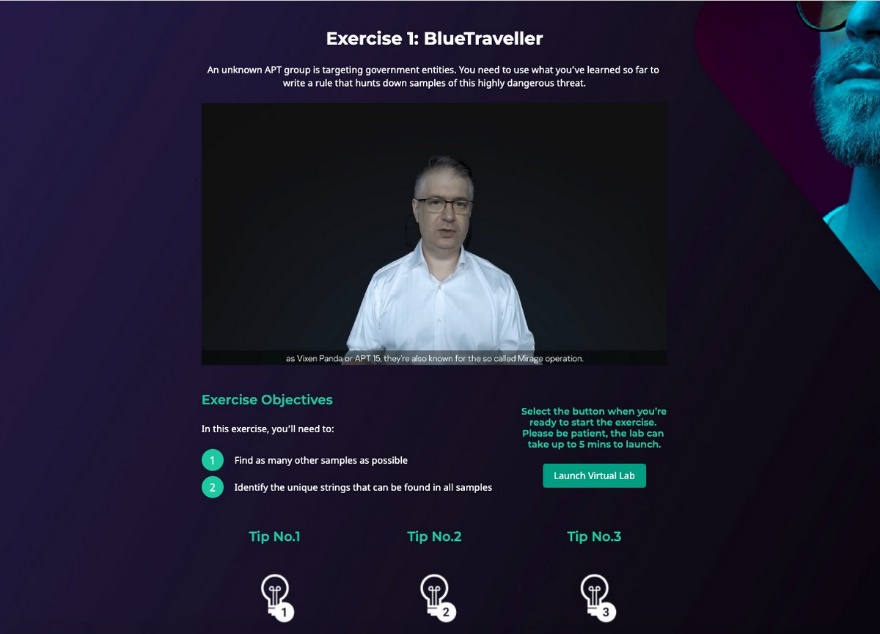
A combination of both theory and hands-on tasks. There’s a virtual lab for training in writing rules and searching for malware samples in our collection.
Practical exercises based on examples of real cyberespionage attacks.
A module about the art of looking for something about which you’ve no precise knowledge, when intuition tells you cyberevil is lurking somewhere but you don’t know where or which cyberevil in particular.
A certificate on completion confirming your new status as a YARA ninja. As previous graduates have told us, it really does help in their career.
So, there you have it, folks: another extremely useful potential string in your bow for fighting highly sophisticated cyberthreats. Meanwhile, it’s business as usual here at K, where we continue our cyberdetective work so we’ll be able to share still more of our very latest know-how and practical experience in fighting the good fight.
 training
training

 Tips
Tips