Since last year, there is no doubt that it’s possible to take control over a connected car remotely. Despite this, we can see zero uncontrolled cars on the streets that obey only to long-distance hackers. So, is it a real threat or a hypothetical possibility?
Judging by debates at RSA 2016, the answer is complex. Right now the threat is at minimum, but it’s going to increase with time. In several years the situation will be far more dangerous. What’s worse, car industry is organized in such a way that manufacturers would probably be solving these fundamental problems for decades. So if we don’t want to lose the rush completely, it’s high time to act; fortunately, many manufacturers understand that as well.
No need for panic…
…But if you want to lift your adrenalin, watch the video taken by the Wired team and the duo of most famous autohackers, Charlie Miller and Chris Valasek.
In the video, you’ll find the Wired editor Andy Greenberg, driving a brand new Jeep. At the same time Miller and Valasek remotely hack Andy’s car: they turn on the radio and the wipers, brake the car and do their best to show, that the steering, wheels, pedals and brakes have their own independent life. It’s because they are not directly connected — there are a lot of built-in computer systems on the way from one control element to another, that are vulnerable to hackers.
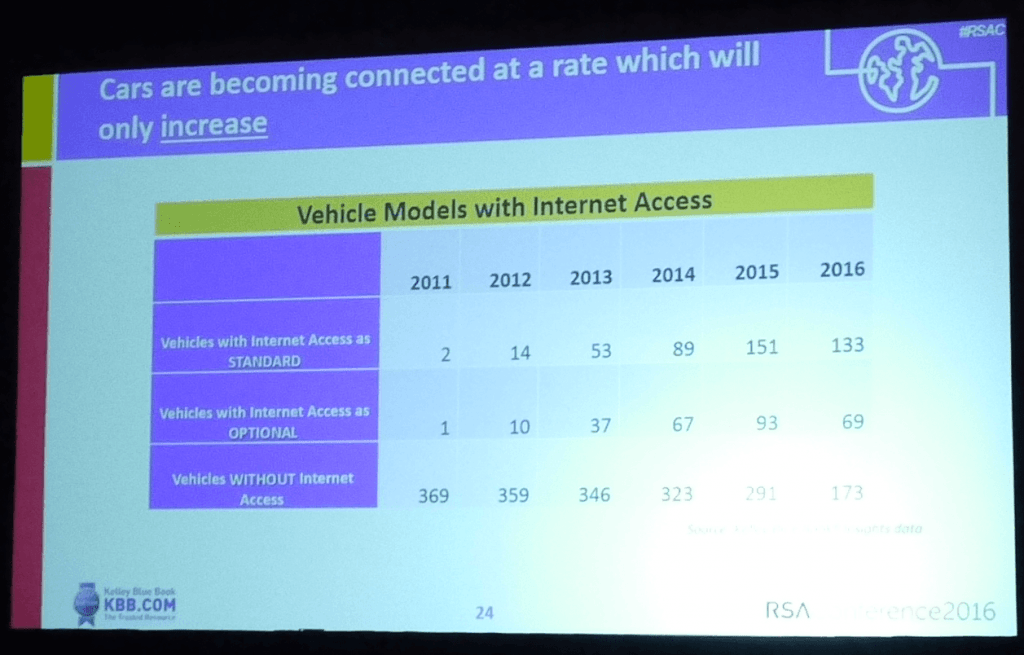
Anyway, only a few modern cars can be tricked in such a way. According to Kelley Blue Book experts, who reported this issue at RSA, average cars driven on US roadways are 11-years old. That’s why the majority of cars are not equipped with Internet or Bluetooth connection and various devices, which could let the hackers in. They are like “dumbphones” compared to smartphones: the domination of “dumbcars” protects all of us from hackers.
#BlackHat 2015: The full story of how that Jeep was hacked https://t.co/y0d6k8UE4n #bhUSA pic.twitter.com/SWulPz4Et7
— Kaspersky (@kaspersky) August 7, 2015
A criminal would have to study out a lot of technologies and devices to hack a connected car. It’s a big and complicated task. That’s not the all: they would also need to invest money into a car and some special equipment. For example, Miller and Valasek studied this topic for four years and in the end learned how to hack only several car models.PCs mostly have same-type processor units (Intel) and only a few OSs (like Windows, OSX, Linux). A car computer system consists of dozens of different specialized computers that interconnect via CANbus.
From one point, it’s bad as such architecture makes it difficult to implement standard security measures, but it also protects us from criminals, who’ll need to spend a great amount of time to understand what is what.
Black Hat and DEF CON: Hacking a chemical plant – https://t.co/KSnCTtLt5U
— Kaspersky (@kaspersky) August 19, 2015
There is no room for complacency
Of course, this plateau period will not last forever. The number of connected cars is constantly increasing. According to Kelley Blue Book, for the last 5 years the amount of cars models connected by default, increased from 2 to 151.
Besides, there are a lot of devices with Internet access, which can be built into even old cars via CANbus. For example, insurance and logistics companies often install trackers that monitor how carefully people drive, where and how often they stop over and other things like this. Such devices can be hacked as well to get the remote access to CANbus and critical car systems.
#Progressive #Snapshot Exposes Drivers to Car Hacking: https://t.co/c8I8lc1zu0
— Kaspersky (@kaspersky) January 27, 2015
The positive dimension is that the number of experts who study this problem is increasing as well. For example, the Open Garages project studies cheap or free hardware and software solutions, which let a user to analyze data from automobile network and interfere into its work. Besides, OpenGarages has contacts of garages, where you can find autos, tools and other infrastructure for testing new software and ideas.The simplest equipment for CANbus study are based on Raspberry Pi or Arduino. Together with accessories, they cost about $100. There are even open source apps for that of different functionality range; some of them are even free. This means, that the number of known vulnerabilities and decrypted sub-network control protocols will increase, and what’s quite possible, very quickly. Malicious application of this knowledge is only the question of time.
Time to act
There are no simple solutions for this problem like install an antivirus to the main computer system. CANbus is a standard protocol, which originates from the 80s. It allows all the systems interconnect without authentication. If you want to improve it, you’ll have to change almost all systems of your car. This work is very likely to be done: though now we know only about one or two incidents of car hacks, a recall of cars has already caused millions damage among manufacturers. After the Cherokee hack, Fiat Chrysler recalled 1.4 million cars.
Another goad for manufacturers is that, as Kelley Blue Book reports, the majority of surveyed people think that manufacturers are to provide them with a security system, not an auto dealer or a third party organization.
Fiat Chrysler Recalls 1.4 million Cars After Software Bug is Revealed: https://t.co/0G9HKy10DI
— Kaspersky (@kaspersky) July 24, 2015
At the same time the car industry has little to no experience in developing protective solutions for their autos. The situation is the same for manufacturers of car components, who also face the same problem.Fortunately, security experts and companies are familiar with these problems, as they have already gone down that path during the last ten years. The IAmTheCavalry project recommends to accept a five-star safety program, which gives a star for every security measure, implemented properly. So we can say that there are five major problems to be solved:
1. Secure Software Development Lifecycle, or safety by design
This means that you develop a car following basic security principles: your projects are standard based to ensure more predictable, normalized and comprehensive practices. Your hardware and software supply chains are all well-governed and traceable to make it easier to remedy any defects. The attack surface and complexity of your code is systematically reduced. And finally, you regularly invite specialists for independent, adversarial resilience testing.
So, how did #Dieselgate actually happen? A look under the hood: https://t.co/WEUi1cnIJT #autohacking pic.twitter.com/HTobFIrg9L
— Kaspersky (@kaspersky) January 6, 2016
2. Third party collaboration
This means that all researchers who have found a vulnerability, should know what’ll come after they report their findings. They must not be threatened by court. Instead, rewards and bounty programs are much welcomed. For example, Tesla already rewards experts who find vulnerabilities in their cars but it’s not yet a widespread practice in the car industry.
Tesla Model S being hacked and patched blazing-fast https://t.co/ZuC0uzeKfn pic.twitter.com/al9naQnsbx
— Kaspersky (@kaspersky) August 10, 2015
3. Evidence capture
Until a car has a “black box”, it will be hard to investigate an incident and gather any proof of hacking. Such black boxes should keep the records of CANbus data exchange. At the same time, privacy concerns should also be taken into account: this data should not be transferred anywhere.
What is a plane's "black box" really? https://t.co/cXLa0FE3ba #airplanes pic.twitter.com/3iCiJ9m6sm
— Kaspersky (@kaspersky) November 12, 2015
4. Security updates
If your car is vulnerable to hackers, you can solve this problem only at a car-care center. Of course, this complicates the update process. Obviously, a number of people did not install these updates at all. That’s why OpenGarages recommends to create an “on the fly” update system — just like the Apple’s solution, implemented in iPhones.
Main components of such systems are secure updating solutions, proper service level agreements and the robust clients’ notification program.
5. Segmentation and isolation
Critical and non-critical systems should be independent, so that criminals could not break the whole car by hacking an infotainment application. It’s also necessary to implement techniques that indicate when a system has been compromised.
Unfortunately, all these measures at best can be implemented in cars, that will be developed in a few coming years. So we’ll see the first secured cars even later. Meanwhile, the number of vulnerable cars is increasing and they are going to stay on roads for ten years or longer. That’s why you don’t need to worry right now, but very soon you’ll have some reasons. And that’s why manufacturers need to act right now.
We at Kaspersky Lab take part in the development process as well. We work with huge car parts manufacturers and automakers to help them develop cars that are secured by design. Our secure OS helps to overcome this challenge a lot.
 auto
auto

 Tips
Tips