Cyber-physical security researchers Marina Krotofil and Jason Larsen presented their research on hacking chemical plants at Black Hat and DEF CON – this was a very fascinating talk.
It’s not that hacking a chemical plant topic itself is unbelievable. Especially when people can hack, say, the uranium enrichment facility, sniper rifle, or thousands of Jeeps at once, there’s no doubt that some other people can hack chemical plant. There’s nothing unhackable in this world, so why should chemical plants should be the exception?
#BlackHat 2015: The full story of how that Jeep was hacked https://t.co/y0d6k8UE4n #bhUSA pic.twitter.com/SWulPz4Et7
— Kaspersky (@kaspersky) August 7, 2015
What is really interesting: in her talk, Krotofil went into depth of what hackers could and should do after taking control over plant’s computer network. First lesson of this research: the aftermath of hack doesn’t have to be obvious.There are multiple ways to exploit a hacked and owned chemical plant. Only one of them is really evident: hackers in question put the plant out of operation. In this case, the aftermath would be hard to miss.
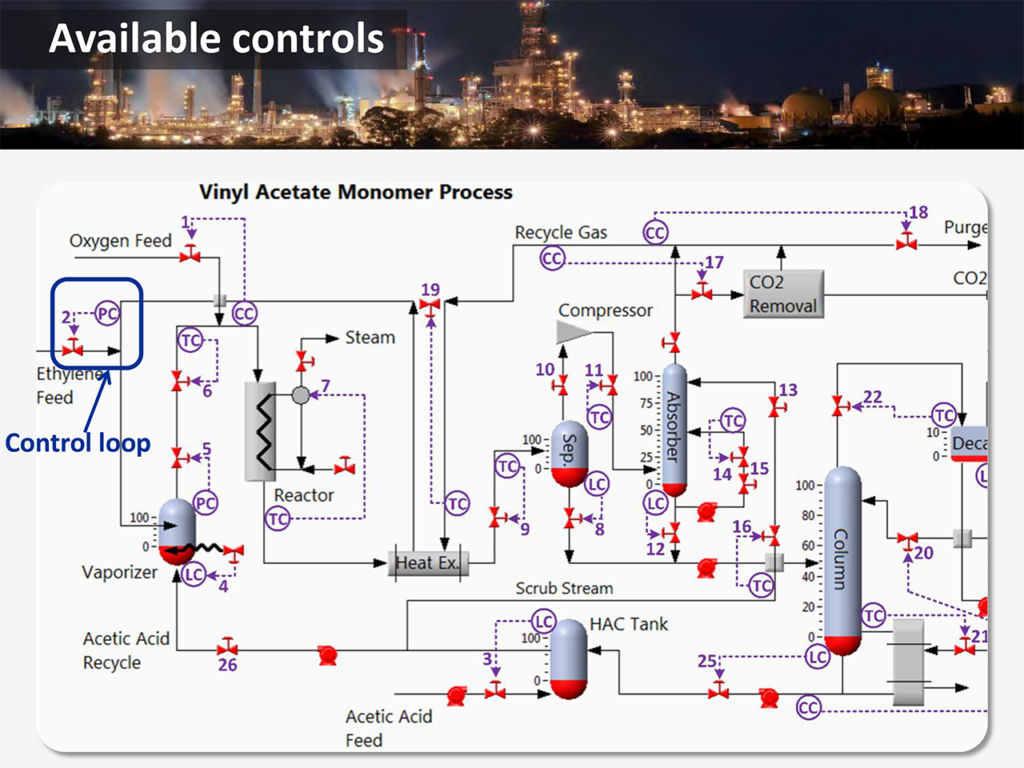
The more refined way of hacking would be to carefully adjust chemical processes in order to make the plant less profitable and the owner company less competitive. For example, hackers can tune chemical process to reduce product quality and/or product rate. And when you speak about chemistry, the parameter that matters the most is purity.
For example, paracetomol with purity of 98% costs just about 1 EUR per kilogram (approximately $1.11 USD). At the same time, paracetomol with purity of 100% costs more than 8000 EUR per kilogram. And this reduction is very clear aim for a hacker who wants to earn money from plant’s owner competitors.
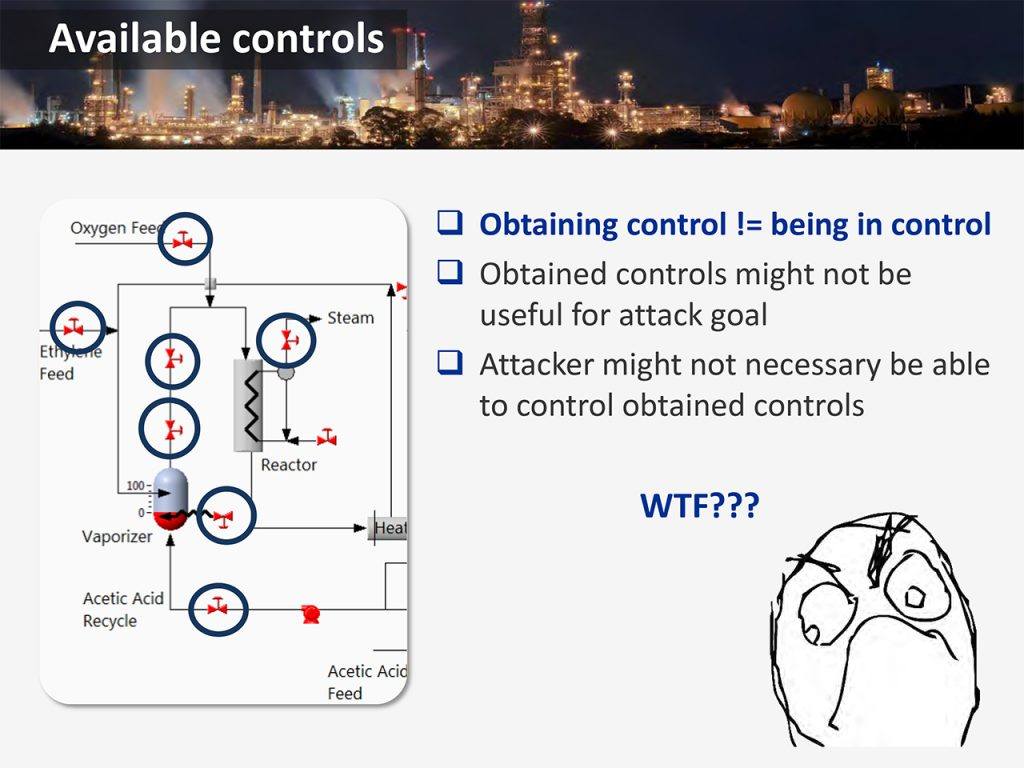
But it’s not that easy to exploit the hack of cyber-physical system, and this is the second lesson we can learn from this research. The plant is very complex thing, and many of its physical and chemical processes depend on each other. If you change something here, something else can happen there. In order to achieve certain goals, you have to understand all these interrelations.
First of all, you need a chemist, a good one to be precise. Secondly, you need your own chemical plant to carry out experiments. By the way, this was the case for Stuxnet developers — they used a few real uranium enrichment centrifuges during development of this famous worm.
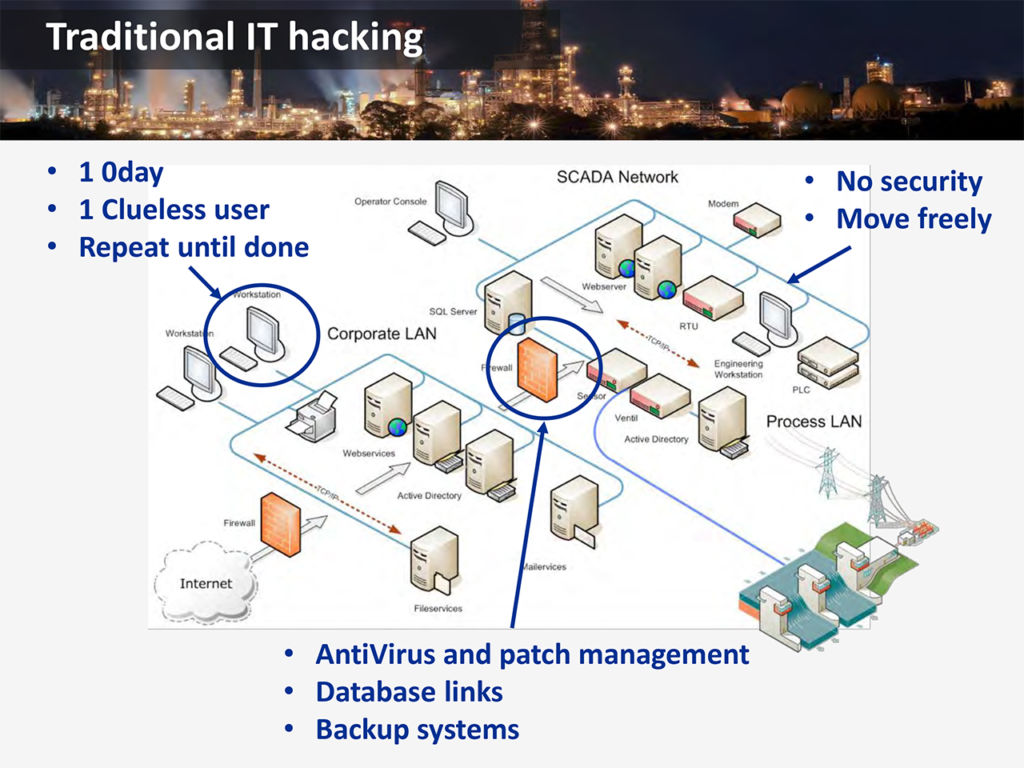
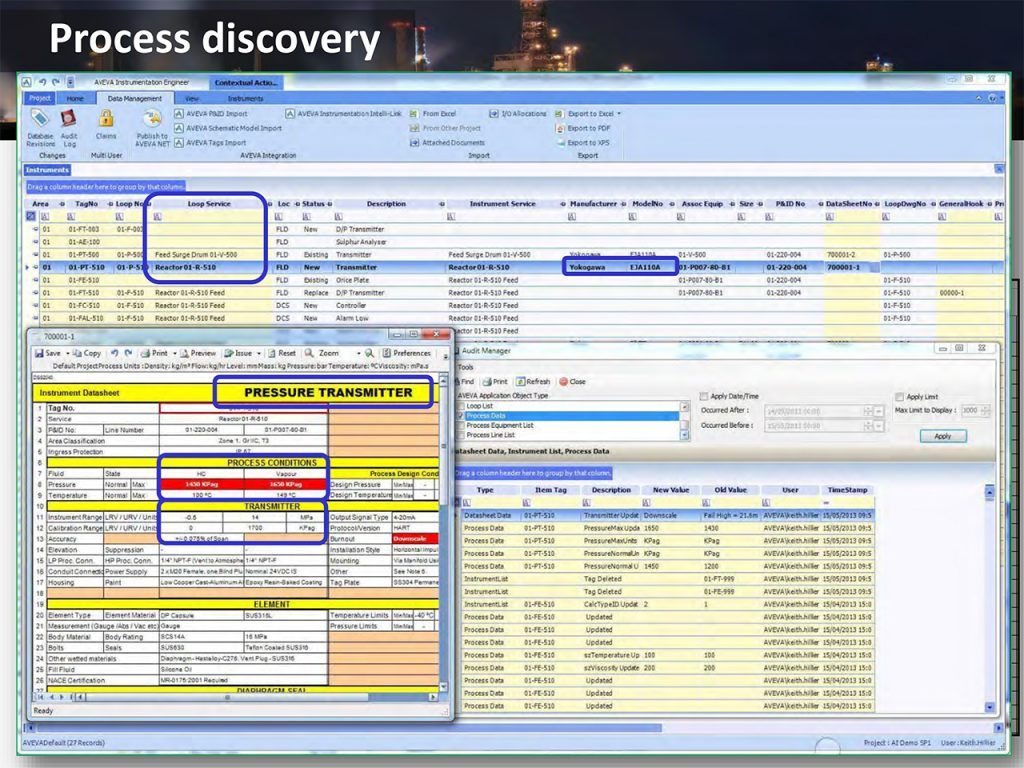
If you can’t afford your own chemical plant, then you need to build a software model and carry experiments there. You will also need to discover, what equipment and software you’re going to deal with. Surprisingly, a hacker’s best weapon in this case is the Internet as a whole, and social networks in particular: it is difficult to imagine what employees do not post there. What they most certainly do post are real screenshots with useful information.
Even after obtaining a real good chemist, all necessary information and software models, you can’t be sure you really can control the chemical processes you want. The thing is, chemical plants aren’t designed to be comfortably hackable; for example cyber-physical systems don’t have versatile diagnostic tools in contrast with pure computer systems, which almost always do have them.
That’s why your adjustments have to be guided by indirect data. For instance, you can’t measure purity of product itself, just because at plants they don’t need such embedded tool, they measure purity after production. Instead you need to estimate it from temperature or pressure. Therefore the complexity of hacking a chemical plant can barely be overestimated. However, if you have plenty of time and resources, everything is possible.
Simply put, it’s rather hard to hack complex cyber-physical systems, on the one hand. On the other hand, it is possible to do. And if the plant is hacked, the complexity plays against defenders as well — it’s not easy for them to detect malicious activity.
What we can learn from chemical plant #hack #BlackHat #DefCon
As Kim Zetter wrote in ‘Countdown to Zero Day‘ book about Stuxnet, originally this worm was designed not to wreck uranium enrichment centrifuges, but to reduce the ‘quality’ of nuclear fuel. And if one very powerful person was patient enough and didn’t insist on faster effect, the malware could stay unnoticed.
 black hat
black hat

 Tips
Tips